ISO 27001 for Third-Party Risk in Healthcare
Post Summary
Healthcare organizations rely on third-party vendors for critical services like electronic health records and medical devices, but these partnerships come with cybersecurity risks. With over 1,300 vendors on average, weak vendor management can expose patient data to breaches, resulting in HIPAA violations and financial penalties. Traditional methods, like annual assessments, often fail to address these challenges.
ISO 27001, a global information security standard, offers a structured approach to managing third-party risks. It includes controls for vendor compliance, secure data sharing, and ongoing monitoring. However, achieving certification can be time-intensive and requires tailoring for healthcare-specific needs.
Censinet RiskOps™, designed for healthcare, automates vendor risk management in line with ISO 27001. It reduces manual processes, speeds up assessments, and provides real-time monitoring, making it easier to secure patient data and meet compliance requirements.
Key Takeaways:
- ISO 27001: Offers a detailed security framework but requires significant effort to implement.
- Censinet RiskOps™: Automates vendor risk management, tailored for healthcare, saving time and improving efficiency.
- Best Approach: A combination of ISO 27001 certification and Censinet RiskOps™ automation ensures both rigorous security and operational efficiency.
Choosing the right strategy depends on your organization's resources, security maturity, and vendor complexity.
1. ISO 27001 Third-Party Risk Management
ISO 27001 provides a structured approach to managing vendor relationships, focusing on compliance, secure data exchanges, and ongoing monitoring.
Vendor Compliance
ISO 27001 includes specific guidelines for handling vendor relationships. For instance, Control A.5.19 requires organizations to establish clear information security policies for all supplier interactions before any data is shared. In the healthcare sector, this means addressing supply chain security challenges by documenting security expectations to ensure vendors meet necessary standards. Control A.5.20 takes it a step further by requiring these security requirements to be explicitly stated in supplier agreements, creating a formal framework for data protection. These steps are essential for building a foundation of trust and security in vendor partnerships.
Secure Data Sharing
A 2021 survey reported that 60% of organizations suffered data breaches linked to third-party vendors [1]. ISO 27001 tackles this issue through Clause 13, which focuses on Communications Security. Control A.13.2.1 emphasizes the need for policies that define encryption, authentication, and secure transmission for sensitive data. Control A.13.2.2 adds another layer by requiring formal agreements that spell out secure data transfer procedures. Additionally, Control A.5.21 ensures that technology suppliers maintain agreed-upon security standards throughout the supply chain. These detailed protocols, combined with ongoing monitoring, address the risks tied to data sharing with external parties.
Risk Assessment and Monitoring
Managing vendor risks isn’t a one-and-done task - it’s a continuous effort. Control A.5.22 calls for regular monitoring, reviews, and updates to vendor services. Healthcare organizations, in particular, must confirm vendor compliance through evidence like audit reports, penetration tests, and incident records. This ongoing vigilance helps ensure that security measures remain effective over time.
sbb-itb-535baee
2. Censinet RiskOps™ Platform

The Censinet RiskOps™ Platform is designed to simplify third-party risk management for healthcare organizations, aligning with ISO 27001 standards. Its purpose is to protect patient care and data, PHI (Protected Health Information), and medical devices by streamlining compliance across vendor relationships.
Vendor Compliance
With Censinet Connect™, organizations can automate risk evaluations for all third-party vendors. This directly supports ISO 27001's standards for defining and enforcing security measures in supplier agreements. Meanwhile, Censinet AI™ speeds up the process by enabling vendors to instantly complete questionnaires while summarizing crucial evidence, product integrations, and even risks associated with their own suppliers.
Secure Data Sharing
Third-party breaches are a common challenge in healthcare. Censinet RiskOps™ addresses this by using a collaborative risk network that facilitates secure exchanges of security documentation and compliance evidence between healthcare organizations and their vendors. It ensures that formal agreements cover essential aspects like data transfer procedures, encryption standards, and authentication protocols.
Risk Assessment and Monitoring
The platform's command center provides real-time risk visualization, allowing organizations to continuously monitor vendor security postures. Automated workflows make it easier to track compliance, while tools like audit reports, penetration tests, and incident records align with ISO 27001's focus on ongoing reviews. A human-in-the-loop approach ensures risk teams maintain control through customizable rules and review processes, enabling proactive risk management.
Risk Treatment and Scalability
Censinet RiskOps™ serves as a central hub for routing assessments and tasks to the right stakeholders for review and approval. Automated workflows across GRC teams ensure swift responses to critical issues. This approach allows healthcare organizations to effectively manage an expanding number of vendors without compromising on security or compliance.
Pros and Cons
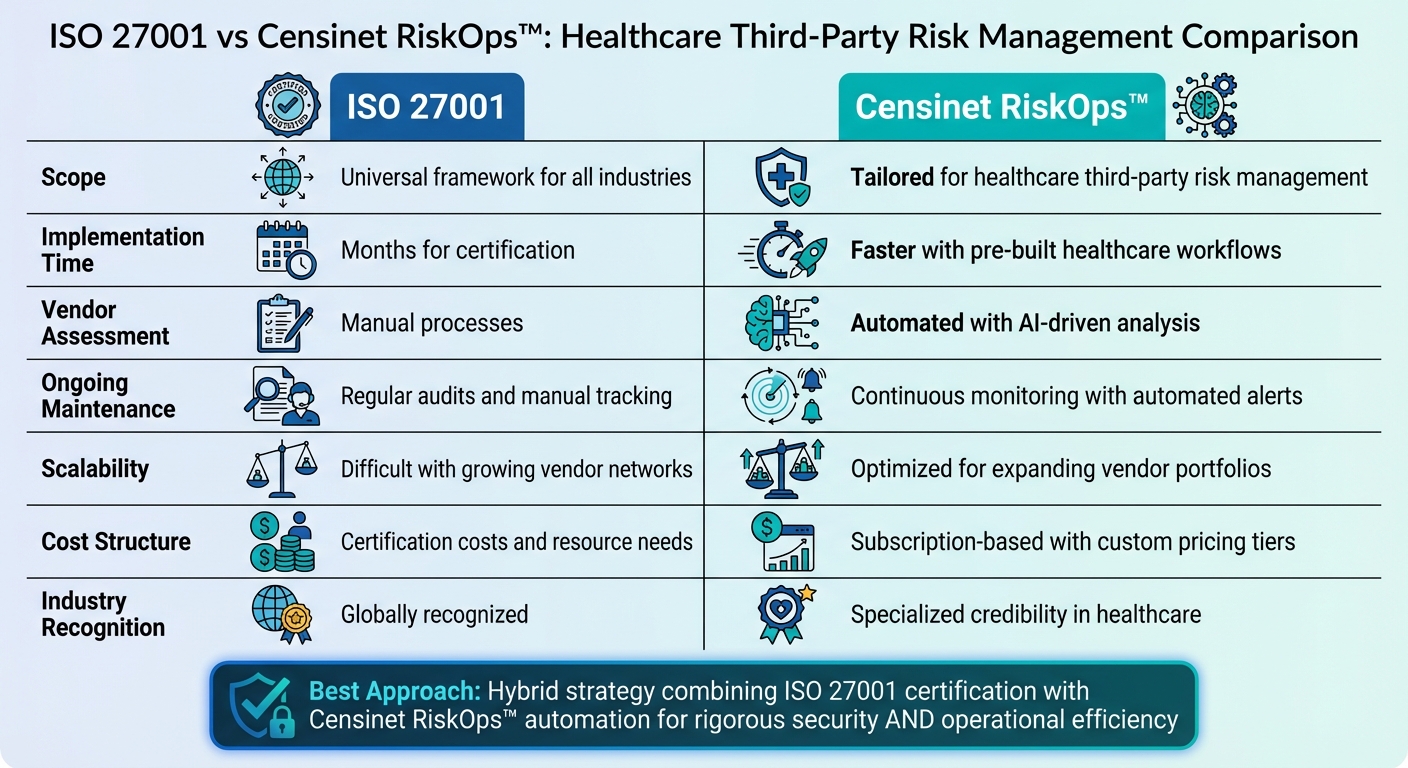
ISO 27001 vs Censinet RiskOps for Healthcare Third-Party Risk Management
Building on the detailed ISO 27001 controls and the capabilities of Censinet RiskOps™, this section explores their strengths and limitations.
Both ISO 27001 and Censinet RiskOps™ bring distinct benefits and challenges to healthcare organizations managing third-party risks.
ISO 27001 offers a globally acknowledged framework that boosts credibility with vendors and regulators. The 2022 update introduced 11 new controls to address modern security threats, making it more applicable to today’s risks [1]. However, achieving certification demands a significant investment of time and resources. Organizations often spend months documenting procedures, conducting internal audits, and preparing for external assessments. Additionally, since ISO 27001 is industry-agnostic, healthcare organizations must adapt its controls to specific needs, such as securing medical devices or protecting PHI.
Censinet RiskOps™, on the other hand, simplifies these challenges by translating ISO 27001 requirements into healthcare-specific automated workflows. Vendor assessments are streamlined using Censinet AI™, reducing evaluation times from weeks to seconds. Its centralized command center provides real-time insights across vendor relationships, far surpassing traditional spreadsheet-based methods.
The platform’s focus on healthcare means it’s equipped to handle complexities like HIPAA compliance, medical device risks, and clinical application security, eliminating much of the need for customization. However, organizations still require internal expertise to configure rules, review AI-generated insights, and make final risk decisions. This "human-in-the-loop" approach ensures accuracy but demands dedicated staff time, reinforcing the earlier discussion on the importance of continuous monitoring.
| Aspect | ISO 27001 | Censinet RiskOps™ |
|---|---|---|
| Scope | Universal framework for all industries | Tailored for healthcare third-party risk management |
| Implementation Time | Months for certification | Faster with pre-built healthcare workflows |
| Vendor Assessment | Manual processes | Automated with AI-driven analysis |
| Ongoing Maintenance | Regular audits and manual tracking | Continuous monitoring with automated alerts |
| Scalability | Difficult with growing vendor networks | Optimized for expanding vendor portfolios |
| Cost Structure | Certification costs and resource needs | Subscription-based with custom pricing tiers |
| Industry Recognition | Globally recognized | Specialized credibility in healthcare |
This comparison highlights the trade-offs healthcare organizations face when balancing the thoroughness of a global framework with the efficiency of tailored technological solutions.
Conclusion
The discussion above highlights how ISO 27001 and Censinet RiskOps™ tackle third-party cybersecurity risks in healthcare, offering distinct advantages depending on an organization's goals and needs.
For healthcare organizations aiming for global recognition and a structured approach, ISO 27001 provides a trusted framework. It’s especially beneficial for those with mature security programs ready to invest the time and effort required for certification. While it’s a strong foundation for security, it does demand significant customization to address healthcare-specific concerns like protecting PHI and securing medical devices. Certification also integrates third-party risk management into the broader Information Security Management System, helping identify vulnerabilities early.
On the other hand, Censinet RiskOps™ is tailored for healthcare organizations that need speed and automation in managing vendor risks. Designed specifically for the healthcare sector, it reduces the complexity of customization and offers real-time insights into vendor risks. By cutting assessment times from weeks to seconds, it eliminates the delays often associated with manual processes tied to ISO 27001.
For many organizations, a hybrid approach works best. Combining ISO 27001 certification with the automation capabilities of Censinet RiskOps™ allows healthcare organizations to benefit from both the rigorous standards of a globally recognized framework and the efficiency of a healthcare-focused solution. This balance ensures thorough security practices while streamlining compliance and vendor assessments. This approach has helped organizations like Emory Healthcare achieve a more scalable TPRM program.
No matter the approach, executive leadership is key. Effective third-party risk management requires clear priorities, dedicated resources, and a commitment to ongoing monitoring and documentation. Organizations must assess their security maturity, available resources, and vendor portfolio complexities to decide on the best strategy - or mix of strategies - to meet their cybersecurity objectives. Aligning these factors is essential for maintaining secure and resilient healthcare operations.
FAQs
Which ISO 27001 controls cover vendor compliance in healthcare?
ISO 27001 outlines specific measures for handling vendor compliance in healthcare. It emphasizes risk assessment, security controls, and third-party risk management. These steps are designed to identify and address potential risks tied to vendors, suppliers, and external collaborators, ensuring they adhere to necessary security standards.
How does ISO 27001 secure PHI when sharing data with vendors?
ISO 27001 plays a key role in protecting PHI (Protected Health Information) when sharing data with vendors. It does this by requiring strict security controls, performing risk assessments to uncover potential vulnerabilities, and ensuring vendors implement safeguards that align with regulations like HIPAA. These steps help maintain secure data exchanges and lower the chances of breaches.
What evidence should we collect to continuously monitor vendor security?
To keep an eye on vendor security at all times, healthcare organizations should focus on collecting real-time data about vendor access, conducting regular security audits, and keeping tabs on compliance status. Using automated tools like Censinet RiskOps™ can make ongoing risk assessments easier and help identify potential threats more efficiently.


