How GDPR Impacts IoT Data in Healthcare
Post Summary
Any IoT telemetry that links to an identified or identifiable person — including device IDs, location data, or usage patterns — qualifies as personal data under GDPR, and health data collected by wearables or monitors is additionally classified as special category data requiring heightened protection.
Yes - GDPR's extraterritorial scope means any organization handling personal data of EU residents must comply regardless of location, making U.S. providers who treat EU patients, conduct international research, or transfer EU patient data subject to GDPR obligations and its penalties.
GDPR requires data minimization at the sensor level, Privacy by Design and Default under Article 25, technical security measures including end-to-end encryption and role-based access control under Article 32, Data Protection Impact Assessments for high-risk processing, and support for patient data rights including access, erasure, and portability.
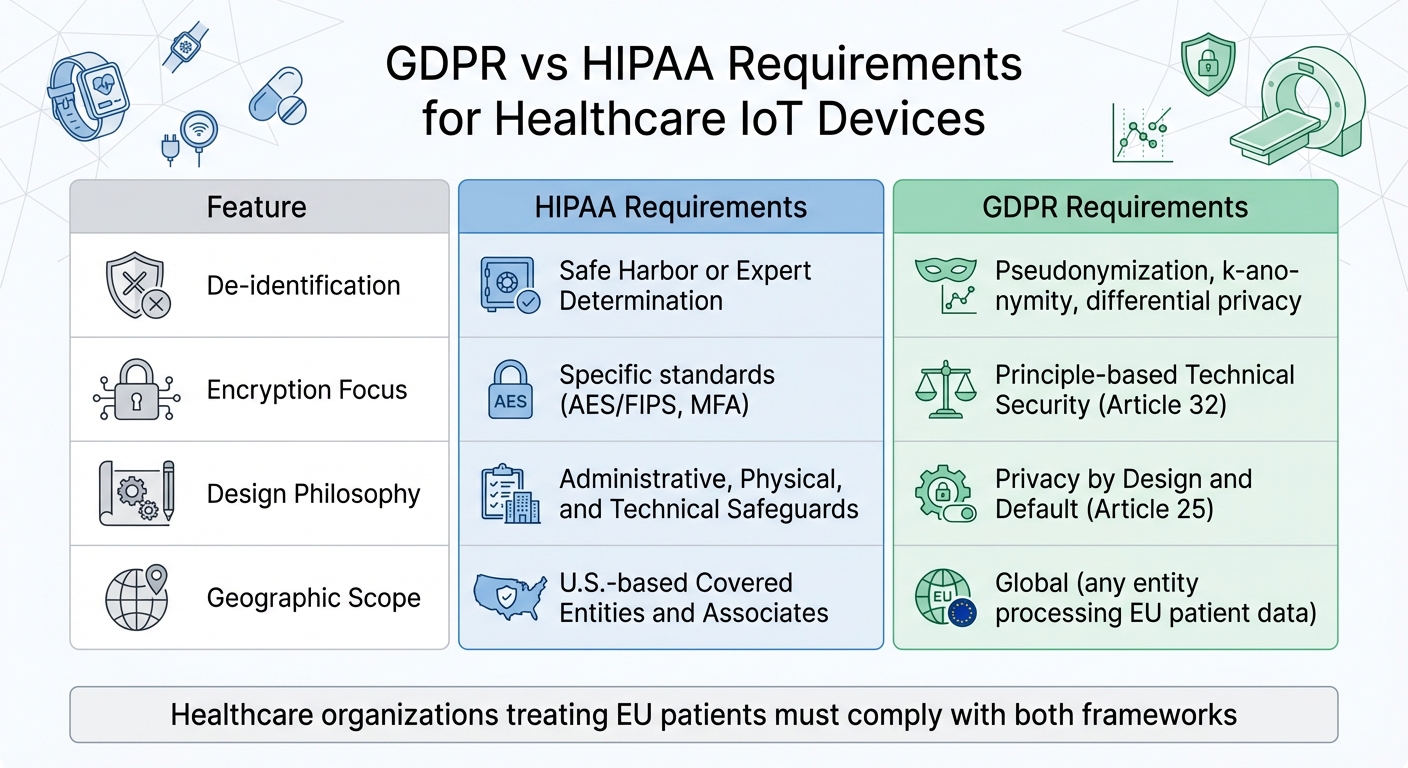
GDPR requires explicit consent for data collection, uses principle-based security standards emphasizing pseudonymization and Privacy by Design, and applies globally - while HIPAA uses specific encryption standards like AES/FIPS, relies on de-identification methods like Safe Harbor, and applies only to U.S. covered entities and their associates.
A DPIA is a mandatory risk assessment under GDPR Article 35 required whenever IoT processing activities pose a high risk to patient privacy — including continuous wearable monitoring, large-scale biometric or genetic data processing, and intensive care patient tracking — and must be updated whenever processing activities or risk profiles change.
Common gaps include outdated encryption standards, weak key management, missing multi-factor authentication, insecure APIs, supply chain vulnerabilities from third-party components lacking SBOMs, and legacy devices that lack pseudonymization or automated data minimization capabilities - leaving them non-compliant with GDPR's Secure by Design expectations.
GDPR has strict rules for healthcare IoT devices like wearables and monitors that collect patient data. The regulation applies to any organization handling data tied to EU residents, regardless of location. Key points:
To comply, organizations must conduct third-party risk assessments, secure data with encryption, and follow GDPR principles like data minimization and purpose limitation.
GDPR Principles That Apply to IoT Data Processing
To ensure compliance from the ground up, GDPR principles must be woven into every aspect of IoT data processing. For healthcare IoT systems, adherence to Article 5's core principles - lawfulness, fairness, transparency, purpose limitation, data minimization, accuracy, storage limitation, and integrity/confidentiality - is non-negotiable [4]. This is especially critical given that 89% of healthcare organizations rely on vulnerable smart medical devices [4]. These principles guide how IoT devices are designed, implemented, and maintained over their lifespan. Below, we'll explore how data minimization, privacy by design, and technical security measures collectively uphold GDPR requirements.
Data Minimization and Purpose Limitation Requirements
Data minimization in healthcare IoT starts with decisions made during the design phase. For example, choices around sampling frequency and payload granularity - whether to stream raw sensor data or only derived metrics - play a key role in ensuring compliance from the outset [1]. These decisions must be made before the devices even reach patients.
Purpose limitation requires organizations to clearly define the lawful basis and specific purpose for collecting each category of data before deployment [1]. This ensures that data is processed only when absolutely necessary. For instance, location data from a wearable device should only be collected if it directly supports the device's medical functionality [5].
To enforce this, organizations should maintain a live data map that tracks data categories, storage locations, and access permissions. This documentation ensures that any data outside the defined scope is excluded, addressing vulnerabilities like unnecessary data collection highlighted earlier [1].
GDPR Article 25: Privacy by Design and Default
Article 25 mandates that privacy considerations aren't an afterthought - they must be built into the system from the start. Healthcare IoT devices should, by default, collect only the data types necessary for their documented purposes, while also limiting storage durations and access permissions [3][1].
One way to achieve this is through pseudonymization, which separates personal identifiers from health-related data. This reduces the risk of re-identification while preserving the data's usefulness [2]. Additionally, wherever possible, devices should prioritize on-device processing, transmitting only processed metrics to cloud servers instead of raw sensor data [3].
For B2B IoT projects, creating an "Evidence Pack" is a practical step. This includes data flow diagrams, key management configurations, and incident response plans, all of which demonstrate that privacy controls are functioning as intended. These artifacts not only help organizations withstand third-party vendor audits but also ensure ongoing compliance throughout the device's lifecycle [1].
GDPR Article 32: Technical Security Requirements
Article 32 focuses on implementing robust security measures. These include encryption (both in transit and at rest), unique credentials for each device, role-based access control (RBAC), multi-factor authentication (MFA), strong key management practices, and network segmentation to isolate IoT/OT systems from IT systems [1][4].
"Data encryption is an essential safeguard for medical devices. As the transferred data flows containing patient information are encrypted, and transferred privately, the possibility of access by a hacker is rendered much more challenging." - MyData-TRUST
Given the long lifespan of IoT devices, systems must support staged rollouts of signed firmware updates to address evolving risks [1]. This also includes having clear end-of-life policies for security patches [3]. Additionally, tamper-resistant audit trails are essential. These logs should capture authentication events, privileged actions, and data access, enabling organizations to reconstruct incident timelines when needed [1]. Such measures directly address the security challenges inherent in healthcare IoT environments.
sbb-itb-535baee
Challenges in Achieving GDPR Compliance for Healthcare IoT
GDPR vs HIPAA Requirements for Healthcare IoT Devices
At first glance, GDPR principles might seem simple. But when applied to the complex world of healthcare IoT, they reveal a web of technical and operational hurdles.
Security Weaknesses in IoT Devices
A significant issue lies in the architecture of many IoT devices, which often fail to meet GDPR's technical requirements. Vendors frequently lag behind modern encryption standards, creating vulnerabilities through weak key management and insufficient identity and access controls. Features like robust multi-factor authentication are often missing, and misconfigured cloud systems or insecure APIs add to the risk of unauthorized access and data breaches.
The problem doesn’t stop there. Supply chain issues, such as outdated firmware or third-party components without a proper Software Bill of Materials (SBOM), further weaken device security. Many legacy devices also lack crucial privacy features like pseudonymization or automated data minimization, which leaves them falling short of GDPR’s "Secure by Design" expectations [2]. On top of these technical flaws, U.S. organizations face additional challenges due to regulatory complexities.
How GDPR Applies to US Healthcare Organizations
The global reach of GDPR compounds these technical issues. Some U.S. healthcare organizations might assume GDPR doesn’t apply to them, but its extraterritorial scope means any organization handling the personal data of EU residents must comply, no matter where they’re located [1][7]. This is particularly relevant in medical tourism, where U.S. providers frequently treat EU citizens. For example, one U.S. medical practice, Farjo Medical Center, treated over 4,000 EU patients in a single year [9].
Unlike HIPAA, GDPR requires explicit consent for data collection from devices, forcing organizations to adopt robust consent management systems. They must also maintain detailed data mapping to trace how data flows - from the IoT device itself, through gateways, and into the cloud [1][6].
Differences Between GDPR and HIPAA for IoT Devices
Healthcare providers operating across borders face the unique challenge of adhering to both GDPR and HIPAA, which have distinct approaches to data security. HIPAA leans on de-identification methods like Safe Harbor or Expert Determination, while GDPR focuses on pseudonymization and advanced techniques such as k-anonymity and differential privacy to reduce re-identification risks.
HIPAA also sets specific encryption standards, requiring technologies like AES/FIPS, strong key management, and multi-factor authentication. Many IoT vendors struggle to meet these requirements [2]. Meanwhile, GDPR's technical mandates are more principle-based (Article 32) and include a proactive approach under Article 25, which emphasizes Privacy by Design and Default. This means that even if a device meets HIPAA’s standards, additional measures - like stronger encryption and enhanced MFA - may still be needed to align with GDPR’s more forward-thinking security framework.
Feature
HIPAA Requirements
GDPR Requirements
De-identification
Safe Harbor or Expert Determination
Pseudonymization, k-anonymity, differential privacy
Encryption Focus
Specific standards (AES/FIPS, MFA)
Principle-based Technical Security (Article 32)
Design Philosophy
Administrative, Physical, and Technical Safeguards
Privacy by Design and Default (Article 25)
Geographic Scope
U.S.-based Covered Entities and Associates
Global (any entity processing EU patient data)
Steps to Achieve GDPR Compliance for Healthcare IoT
Meeting GDPR requirements for IoT devices in healthcare demands a structured approach that balances technical measures with organizational responsibility. These steps address the unique challenges posed by connected medical devices, ensuring both patient data security and accountability.
How to Conduct Data Protection Impact Assessments (DPIAs)
Start by conducting thorough risk assessments. Under GDPR Article 35, DPIAs are mandatory for IoT processing activities that pose a high risk to patient privacy [10]. Examples include monitoring through wearables, continuous patient tracking in intensive care, or large-scale processing of sensitive data like biometric or genetic information. Treat the DPIA as a dynamic document, updating it whenever IoT processing changes or new risks emerge.
Map out all data flows from IoT devices, detailing sources, recipients, storage locations, and any third-party providers involved in data transmission. The Data Protection Officer (DPO) should lead this effort, working closely with IT security, clinical teams, and project managers. Clearly document the legal basis for processing IoT data, whether it’s patient consent or the necessity of delivering healthcare services. If residual risks remain high after mitigation, consult your national Data Protection Authority before proceeding.
Implementing Encryption for IoT Data
After completing DPIAs, focus on securing data through encryption. Use encryption protocols that meet AES and FIPS standards, ensuring strong key management and multi-factor authentication [2]. Employ end-to-end encryption to safeguard data during transmission and storage. Pseudonymization can further reduce the impact of potential breaches while keeping clinical data useful. This aligns with GDPR’s Privacy by Design principles, minimizing re-identification risks.
Additionally, consider adopting a Zero Trust architecture. This approach continuously verifies every access request within the IoT network, regardless of its origin, adding an extra layer of security to sensitive healthcare data.
Using Censinet RiskOps™ for IoT Risk Management

Managing IoT risks across multiple devices and vendors can be complex, but centralized platforms like Censinet RiskOps™ simplify the process. This platform automates third-party and enterprise risk assessments, streamlining medical device security and GDPR compliance.
Censinet RiskOps™ reduces manual tasks by automating vendor risk assessments, summarizing evidence, and generating risk reports. Its human-guided automation ensures critical oversight while scaling operations, routing key findings to the appropriate stakeholders for review. The platform’s centralized dashboard provides real-time updates on IoT-related policies, risks, and tasks, acting as a command center for continuous monitoring and compliance management.
Conclusion
Summary of GDPR Requirements for Healthcare IoT
When it comes to healthcare IoT, integrating GDPR compliance into every layer of your infrastructure is non-negotiable. The moment IoT telemetry connects to an identified or identifiable person - whether through device IDs, location data, or usage patterns - it falls under GDPR’s scope [1][11]. Healthcare organizations must establish a lawful basis for processing under Article 6 and meet additional conditions for handling sensitive health data as outlined in Article 9 [6][11].
Key GDPR principles to follow include data minimization at the sensor level, embedding Privacy by Design during development, and implementing technical safeguards like end-to-end encryption and secure boot processes [1][6][8]. Additionally, systems must support data subject rights such as access, erasure, and portability - extending across all components, from gateways to cloud storage [1][12]. Non-compliance risks hefty penalties [12]. With around 18 billion web-enabled IoT devices worldwide as of 2022 [13], the regulatory exposure for healthcare organizations continues to expand.
Adopting a layered compliance strategy ensures every phase, from data collection to storage, aligns with GDPR requirements.
Recommended Actions for Healthcare Organizations
To align with GDPR:
For managing multiple IoT devices and vendors, consider tools like Censinet RiskOps™. This platform centralizes risk management, automates critical tasks, and provides real-time visibility into IoT-related risks and compliance. It helps healthcare organizations scale their operations without compromising GDPR’s rigorous standards.
FAQs
When does IoT device data count as personal data under GDPR?
Under GDPR, data collected by IoT devices is classified as personal data if it pertains to an identified or identifiable individual. This means any information processed by IoT devices that can directly or indirectly reveal someone's identity - like unique identifiers, usage behaviors, or data tied to specific devices - falls under this category.
Do US healthcare providers have to follow GDPR for EU patients?
US healthcare providers aren't directly obligated to adhere to GDPR when dealing with EU patients. However, if they handle personal data belonging to EU residents - especially during international data transfers - they must ensure compliance with GDPR to avoid hefty fines. Proper safeguards are essential when managing this type of data.
What are the biggest GDPR security must-haves for healthcare IoT devices?
To meet GDPR standards, healthcare IoT devices must follow strict security practices. These include:
These steps not only align with GDPR requirements but also enhance the protection of sensitive patient information.
Related Blog Posts
- GDPR vs. HIPAA: Key Differences for Healthcare
- GDPR vs. HIPAA: Cross-Border Breach Rules
- GDPR Risk Assessment vs. HIPAA Compliance
- How AI Helps Monitor GDPR Compliance in Healthcare
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"When does IoT device data count as personal data under GDPR?","acceptedAnswer":{"@type":"Answer","text":"<p>Under GDPR, data collected by IoT devices is classified as personal data if it pertains to an identified or identifiable individual. This means any information processed by IoT devices that can directly or indirectly reveal someone's identity - like unique identifiers, usage behaviors, or data tied to specific devices - falls under this category.</p>"}},{"@type":"Question","name":"Do US healthcare providers have to follow GDPR for EU patients?","acceptedAnswer":{"@type":"Answer","text":"<p>US healthcare providers aren't directly obligated to adhere to GDPR when dealing with EU patients. However, if they handle personal data belonging to EU residents - especially during international data transfers - they must ensure compliance with GDPR to avoid hefty fines. Proper safeguards are essential when managing this type of data.</p>"}},{"@type":"Question","name":"What are the biggest GDPR security must-haves for healthcare IoT devices?","acceptedAnswer":{"@type":"Answer","text":"<p>To meet GDPR standards, healthcare IoT devices must follow strict security practices. These include:</p> <ul> <li><strong>Privacy-by-Design Principles</strong>: Devices should be designed with patient data privacy as a core consideration from the start.</li> <li><strong>Continuous Cybersecurity Measures</strong>: Ongoing monitoring and updates are essential to address new threats and vulnerabilities.</li> <li><strong>Thorough Risk Assessments</strong>: Regular evaluations help identify and mitigate potential risks to sensitive data.</li> <li><strong>Strong Encryption</strong>: Robust encryption safeguards patient information during storage and transmission.</li> <li><strong>Detailed Record-Keeping</strong>: Maintaining comprehensive records of risk management efforts and security updates ensures accountability and compliance.</li> </ul> <p>These steps not only align with GDPR requirements but also enhance the protection of sensitive patient information.</p>"}}]}
Key Points:
How do GDPR Article 5 core principles apply specifically to healthcare IoT data processing?
- Lawfulness, fairness, and transparency require a documented legal basis under Article 6 before any IoT data collection begins - and for health data, additional conditions under Article 9 must be satisfied, given its classification as special category data
- Purpose limitation means the intended use of every data category must be defined before device deployment, not after - location data from a wearable, for example, is only permissible if it directly supports the device's documented medical function
- Data minimization begins at the design stage through decisions about sampling frequency and payload granularity - organizations must choose whether to stream raw sensor data or only derived metrics, with GDPR favoring the latter wherever clinically viable
- Storage limitation requires automated retention policies that delete or anonymize IoT data once it exceeds its defined storage period - a requirement that many legacy healthcare IoT systems are not architecturally equipped to support
- Integrity and confidentiality mandate that IoT systems protect data against unauthorized access, accidental loss, and destruction throughout the data's lifecycle - from sensor collection through gateway transmission to cloud storage and archival
What does GDPR Article 25 Privacy by Design and Default require from healthcare IoT manufacturers and operators?
- Privacy considerations must be built into devices from the design phase - not retrofitted after deployment - meaning security architecture, data flow, and access controls are compliance requirements at the product development stage, not afterthoughts
- Default settings must collect only minimum necessary data with limited storage durations and restricted access permissions - devices that default to maximum data collection require affirmative configuration changes to reduce collection, inverting the compliance burden
- Pseudonymization - separating personal identifiers from health-related data - is a specifically recommended technique that reduces re-identification risk while preserving the clinical utility of the data for analysis and care delivery
- On-device processing preferred over raw data transmission - where technically feasible, devices should process sensor data locally and transmit only derived metrics to cloud infrastructure, limiting the volume of identifiable health data in transit
- Evidence Pack documentation for B2B IoT deployments - including data flow diagrams, key management configurations, and incident response plans - provides audit-ready proof that Privacy by Design controls are functioning as designed throughout the device lifecycle
How do GDPR and HIPAA differ in their approach to healthcare IoT security and compliance?
- Consent model divergence is the most operationally significant difference - GDPR requires explicit, informed consent for IoT data collection while HIPAA permits data processing under broader treatment, payment, and operations provisions, requiring organizations operating under both frameworks to implement the more restrictive GDPR consent model
- De-identification versus pseudonymization represent distinct technical approaches - HIPAA accepts Safe Harbor or Expert Determination methods, while GDPR specifically requires pseudonymization and encourages advanced techniques such as k-anonymity and differential privacy that provide stronger re-identification protection
- Encryption specificity differs between frameworks - HIPAA mandates specific standards including AES/FIPS and defined key management practices, while GDPR's Article 32 is principle-based, requiring appropriate technical measures without prescribing specific algorithms, meaning GDPR-compliant devices may need to exceed HIPAA's specified standards
- Geographic scope is fundamentally different - HIPAA applies only to U.S. covered entities and business associates, while GDPR's extraterritorial reach means any healthcare organization globally that processes EU resident data must comply, regardless of where the organization is incorporated or operates
- Design philosophy separates the two frameworks at the architectural level - HIPAA organizes requirements around administrative, physical, and technical safeguards applied to existing systems, while GDPR's Privacy by Design mandate requires security to be an original design input, not a compliance layer applied after the fact
What are the most common GDPR compliance gaps in healthcare IoT device deployments?
- Outdated encryption and weak key management remain the most prevalent technical gap - many IoT vendors have not updated device firmware to meet current AES/FIPS standards, leaving data in transit and at rest inadequately protected against modern attack vectors
- Missing or insufficient multi-factor authentication allows unauthorized access to device interfaces and management consoles, a gap that is particularly acute in legacy devices designed before MFA became a standard security expectation
- Supply chain vulnerabilities from third-party components without accompanying SBOMs make it impossible for healthcare organizations to assess the full vulnerability surface of deployed devices - directly undermining GDPR's requirement for comprehensive risk assessment
- Legacy devices lacking pseudonymization or automated data minimization cannot be brought into compliance through configuration changes alone - they require either hardware replacement or compensating network-level controls that add operational complexity and cost
- Insecure APIs and misconfigured cloud integrations create unauthorized data access pathways that bypass device-level controls, representing a systemic gap between GDPR's security expectations and the actual architecture of many deployed healthcare IoT ecosystems
What steps must healthcare organizations take to achieve GDPR compliance for their IoT device portfolios?
- Live data map maintenance documenting current data flows, storage locations, access models, and third-party providers for every IoT device - providing both the operational visibility and the audit evidence that GDPR compliance requires
- Data Protection Impact Assessments conducted before deploying any IoT processing activities that carry high privacy risk, treated as living documents that are updated whenever processing workflows, device configurations, or risk profiles change
- End-to-end encryption implementation meeting AES/FIPS standards with strong key management and MFA across all device interfaces - supplemented by pseudonymization to reduce re-identification risk while preserving clinical data utility
- Zero Trust architecture adoption that continuously verifies every access request within the IoT network regardless of origin — adding a defense-in-depth layer that addresses the reality that perimeter-based security models are insufficient for distributed healthcare IoT environments
- Secure over-the-air update capability established for all deployed devices - given IoT device lifespans that routinely exceed a decade, the ability to deploy signed firmware updates remotely is essential for maintaining GDPR-compliant security posture over time
How does Censinet RiskOps™ support GDPR compliance for healthcare IoT risk management?
- Automated third-party and enterprise risk assessments enable healthcare organizations to evaluate IoT device vendors against GDPR security requirements at scale - identifying compliance gaps across device portfolios without the manual overhead that makes comprehensive assessment operationally unsustainable
- Centralized risk dashboard provides real-time visibility into IoT-related policies, risks, and compliance tasks across the full device portfolio - replacing fragmented spreadsheet-based tracking with a single command center for continuous compliance monitoring
- Evidence summarization and documentation through Censinet AI™ processes vendor security questionnaires and uploaded documentation rapidly, generating risk reports that support DPIA documentation and audit readiness without burdening clinical or IT teams
- Human-guided automation maintains the compliance oversight requirement that neither GDPR nor HIPAA allows to be fully delegated to automated systems - routing critical findings to appropriate stakeholders for review while handling routine assessment tasks automatically
- Scalable operations allow healthcare organizations to manage growing IoT device portfolios and vendor relationships without proportional headcount increases - addressing the operational reality that GDPR compliance obligations scale with device volume in ways that manual processes cannot sustain


